As part of the series � Best Free iPhone Apps for the Geeks, we continue to add apps suitable for the photographer in all of us. To quote from last week�s post � �Apple Store has thousands of useful apps populated under different categories and many of them are free. Many of these free apps expect you to pay when you want to use their advanced features. Surprisingly there are some free apps which are not crippled by design.� I am writing about some of the useful apps aimed at the photographers � which are free. At least they were when I first downloaded them.

�Knowledge is merely having clarity of facts and truths while Wisdom is the practical ability to make consistently good decisions in life.� This blog , like most of the pages of TargetWoman, contains distilled wisdom that can make you arrive at good decisions based on the wide range of information we so assiduously collected for you.
Augustine�s Law Number XVII states that �Software is like entropy. It is difficult to grasp, weighs nothing, and obeys the Second Law of Thermodynamics; i.e., it always increases.� Most of these apps I have added into this page are relatively small in size but are so handy that you will be glad you have them in your phone.
There are tons of camera apps and photo editing apps in Apple Store. Most of them offer basic editing in their app in the free version and offer more advanced features in the paid version. But there are some which offer exceptional photo touching/editing features even in the free version. So in this post, I review only those free apps which offer essential features useful for any serious photographer.
Microsoft Pix :
Microsoft is the leading desktop computer operating System – Windows. And you thought that they would only concentrate on their flagship Windows 10. They have been working on so many other things as well. They have successfully ported their Internet Explorer to iOs. Creating Software is Microsoft’s primary mission in their life.
Many of the new camera apps start on the premise that most of us are just not fast enough to select the right time to click in order to preserve the moment for posterity. They try to seize the moment by taking a series of shots before and after we take the shot. This MS Pix does that for you. It automatically combines a stream of photos before and after you press the button – giving you a best possible image – according to its Artificial Intelligence based algorithm. The AI deduces your subject and tries to adjust the camera settings and tweaks them for the best possible results – at least in theory.
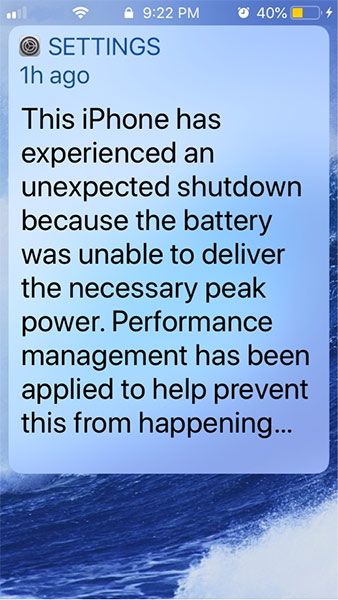
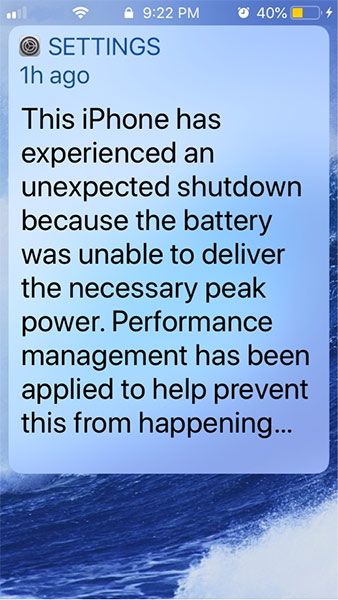
We have tried this app in 2 different iPhones and found drastically varying results. In an iPhone 7, the app sort of worked reasonably well without much ado. On the other hand in an iPhone SE (currently at the low end) it ended up heating up the phone and delivered average results. In repeated usage, it even triggered a shut down. If you have not set the permissions in the settings for accessing your phone�s microphone (required for Video), the app may hang. You may need to do a temporary reset � hold the power button and when you see the �slide to power off� press the Home button.

Microsoft Pix does a reasonably good job when you do a Hyperlapse. It uses stabilized images from the camera to stitch together a time lapse video. It extracts the maximum from the phone�s CPU. It is a power intensive process which hogs the battery too.
Microsoft Pix app at the moment has 2 broad categories of effects � frames and mosaic cartoon effects. You can crop the image with this app and draw a basic frame around the picture. You can share the final image with any of the apple applets.
MS Pix has more in its armory. It is capable of capturing a business card, document and white board – and tries its best to extract text content. Yes – it tries to do Optical Character Recognition (OCR) from the image. For the best results in this role, you would be advised to start with a plain white uncluttered background and black fonts. It recognizes a limited set of fonts. Any fancy font will not be recognized at the moment.
Another feature of this app is it tweaks the image when it notices a face in the image. When the app is running, we could notice that the phones run hotter indicating that it pushes the CPU to its limit – which is not surprising when you run enterprise class AI in a relatively tiny mobile CPU. We were really impressed with some of the results of this MS Pix and they offer this product free for now.
Tip: Always start with a fully charged phone when you want to use this app. Apple iOs might consider the rapid discharge of the phone battery as a malfunction and invoke a shut down. It happened to us many times. Your mileage may vary depending upon the condition of your battery.
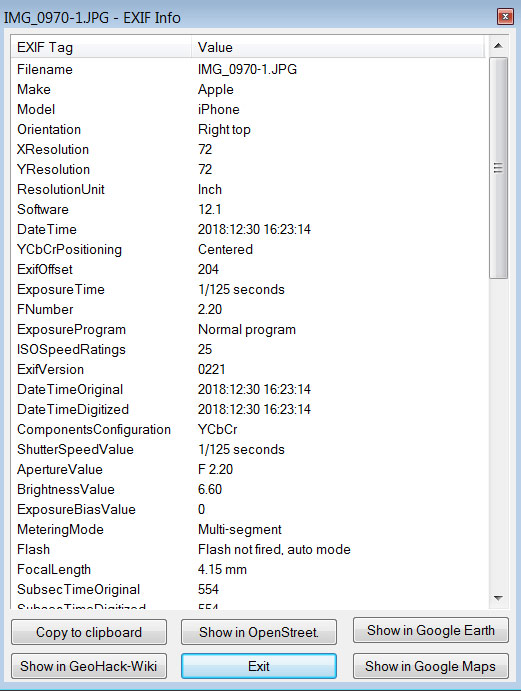
EXIF Metadata
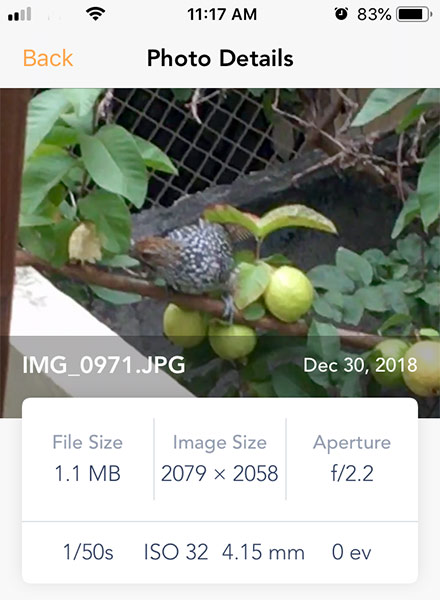
Your digital camera that includes your mobile phone bakes a lot of information along with your shot into the picture at the time of taking the picture. The ‘Exchangeable Image File Format’ EXIF is the industry standard. The information contained there can be invaluable for any photographer or designer. In TargetWoman we have been processing literally several thousand images every year. It is probably the reason why you see we show more number of iOS Apps targeted to Photography and Visual Design.
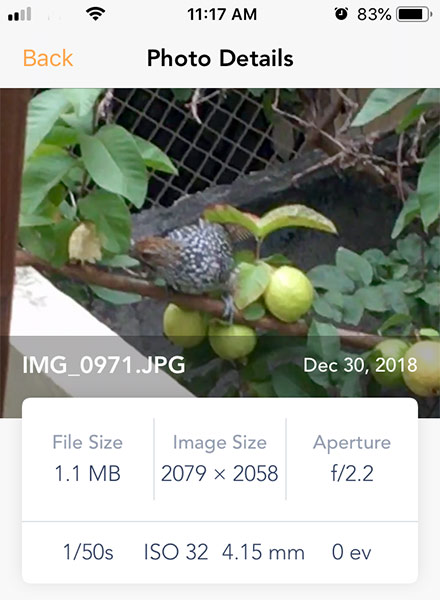
Amongst other things, EXIF data contains GPS data and map location which when you share your photos with others, you may not want to share the GPS location data for reasons of privacy. Or you may want to strip your photos of any telltale EXIF data. The last thing you need is some low life to pry into your shared photo and extract the exact location where you spend quality time with your family. A lot of people don’t realize that that spontaneous selfie they took when they were jogging contained enough information for anyone to know your morning routine. Get into the habit of stripping all metadata before you share a photograph. One day you will thank me for warning you upfront.
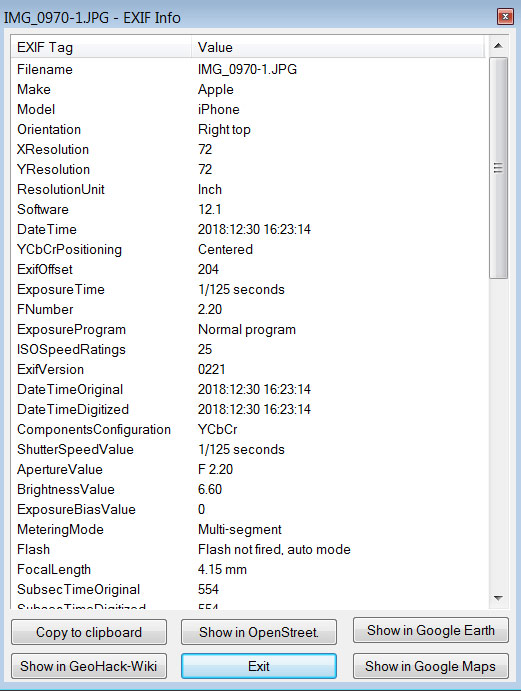
This app allows you to view 50 + metadata tags including your GPS co-ordinates and edit them if you want. And this does with a tiny memory foot print – less than 33 MB.
We have shown the original image and an IrfanView desktop app that shows the EXIF metadata alongside this iOS app here for comparison.
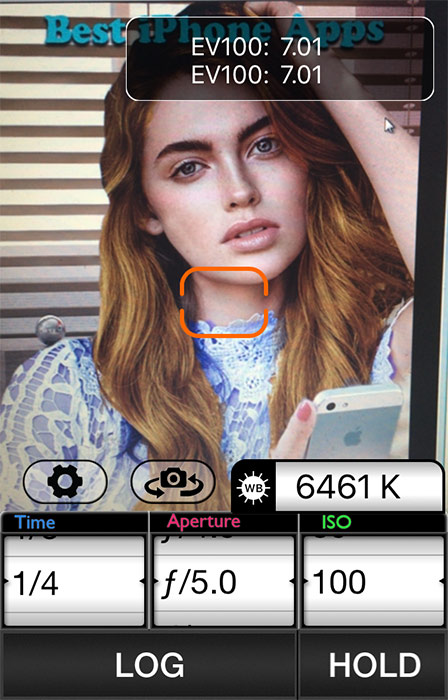
Pocket Light Meter

A light meter is an indispensable tool for a professional photography/Videography. This handy little tool will measure the reflected light and allows for reciprocity calculations. You can use this app along with film cameras as the results are pretty accurate. A reflected light meter measures the light coming from the subject and aids the photographer to decide about the shutter speed and f-number under the given film speed and the settings light. This iOs app, in addition to the shutter speed (time), aperture and film Speed (ISO) also tells you the color temperature in Kelvin. You can adjust the color temperature with your lighting so that the entire photo session can have uniform color temperature for pleasing results.
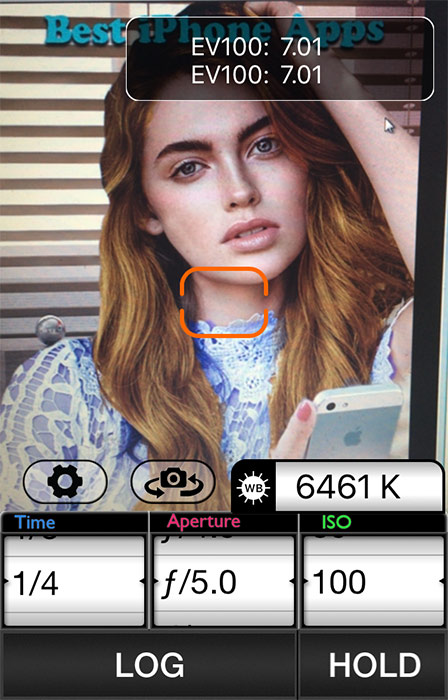
It is not just for the photographers alone that this feature is useful. If you want to measure the color temperature of your home lighting with your newly minted LED lights, this tool can be quite invaluable. Warmer colors are chosen in bedroom and living room (around 3000 K) whereas for Kitchen and study a cooler light will help you to discern better details (5500 K). Your automobile head lights need to be of certain color temperature for maximum visibility which depends on the type of head lights – tungsten halogen, Xenon HID or the LEDs. In the US, generally a head light with 4000 K if Tungsten Halogen or 5000 K if Xenon HID is the most preferred choice.
You can even set the TV/monitor color settings with this app. Set up a white background in your monitor and measure the color temperature in this app – and adjust the color correction from your Graphic Properties applet. I told you sometimes lots of useful things in life come in small sizes.
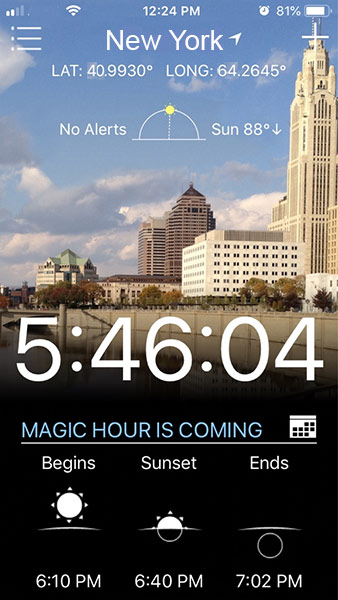
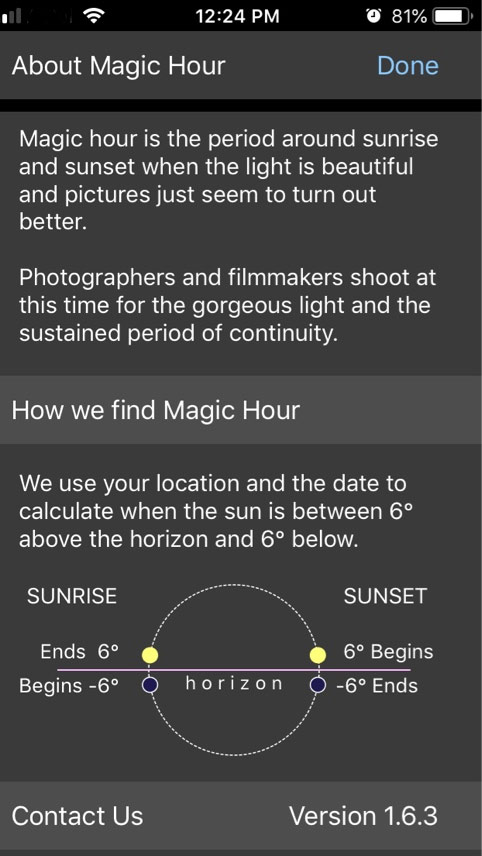
Magic Hour
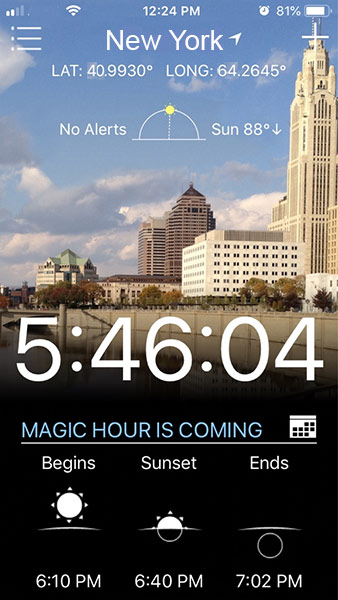
Photography is the art of painting with light. So the critical part is the light – the right light and at the right angle. In outdoor photography, sun light is the primary source but it shines in different colors and in different intensity depending upon the time. The harsh glare of the sun between 10.00 and 3.00 would not be ideal. And the color temperature would be bluish white. On the other hand, during the morning hours and evening hours, the streaming light at a lower angle will be the ideal light for photography. The warm colored sun light will chisel out the details in your subject. The warm glow of the iridescent sun will provide modeling, texture depth, warmth and interest to your photograph. This is why Photographers call these hours as ‘Magic hour’ or Golden hour. A portrait taken at this golden hour will accentuate the glow of the skin. Now that we know what this Magic hour is, how do we find the hour ? It is not all. How do we find the magic hour where we are planning to have the photo shoot ?
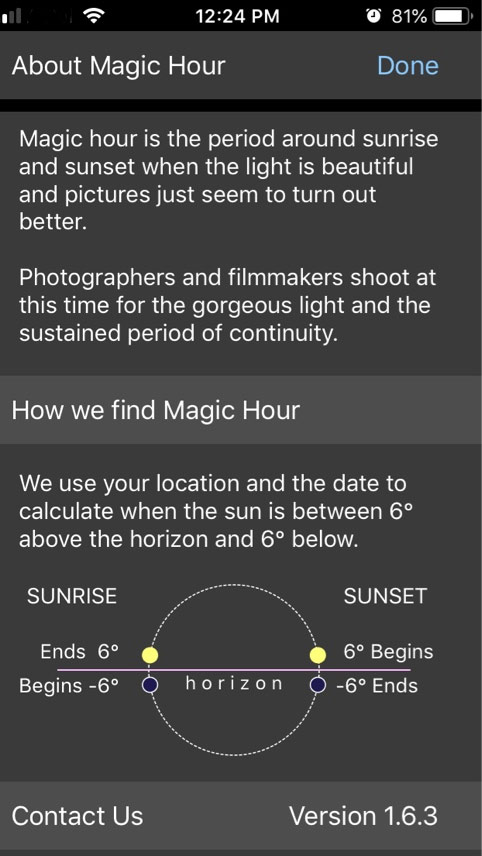
I will quote from the App developers here: ‘Magic Hour (also called golden hour) is the time of day around sunrise and sunset when the light is great for photography and cinematography. It is typically when the sun is between 6 degrees below the horizon to 6 degrees above. This sunlight is evenly dispersed and helps you create great pictures.
Magic Hour 1.6 makes it easy for you to know when magic hour is coming and how much time you have left once it begins. The app takes your location along with the current day and calculates when magic hour will occur.’
This tiny 25 MB app ranks in the top for outdoor photography. It sits there quietly in the iPhone until awakened when needed. Doesn’t ask for pernicious permissions and won’t bug you with notifications.
Snapseed
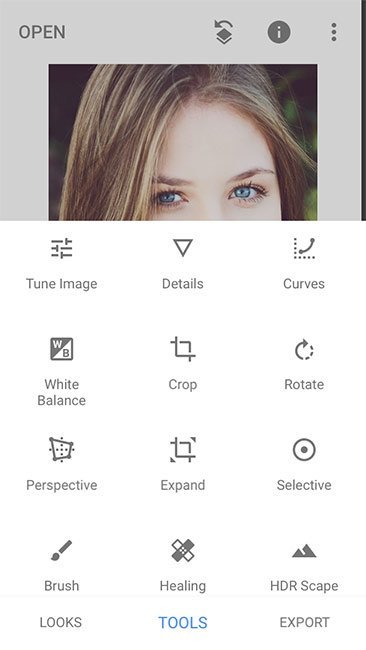
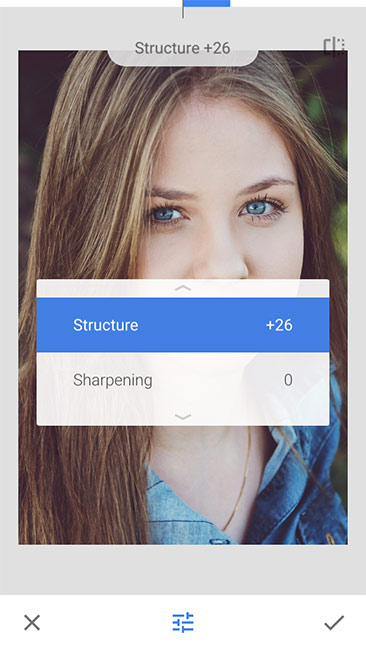
This powerful app from Google is a full featured Photo editing app for iOS as well as for Android. Originally developed by Nik Software, this app provides a plethora of really useful features. You can set the white balance, change the perspective, fine tune the exposure curves, crop the image and do other manipulation right from your phone and what�s more you don�t need to spend a dime.


I have explored some of the major features of this app and as you can see from the results displayed here, they are awesome. You can use many of the functions easily enough instinctively and reserve the rest of the advanced functions to a later date.
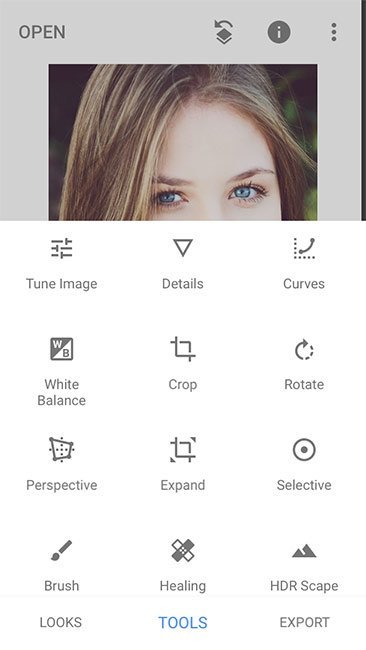
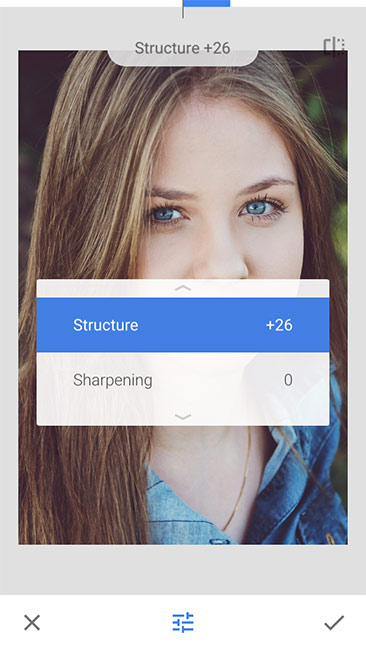
Like I said earlier, I am not too comfortable with large applications in my phone and the size of the app is a critical deciding factor in the selection of apps for this page. Snapseed for all its prowess still weighs around 22 MB � an incredible feat by itself. All the complex functions have been coded within 22 MB and the small size doesn�t cripple the app in any way.
The current version has a size limitation of 20 Mega pixels for iOs � which is plenty at this time.
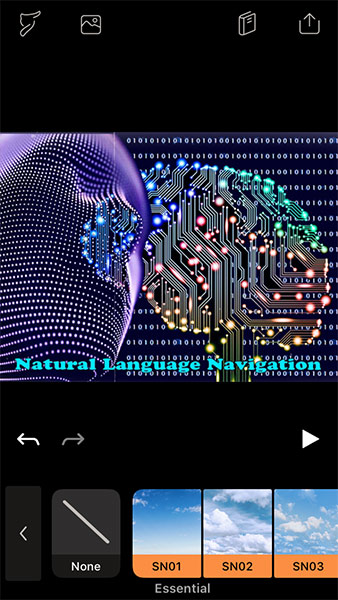
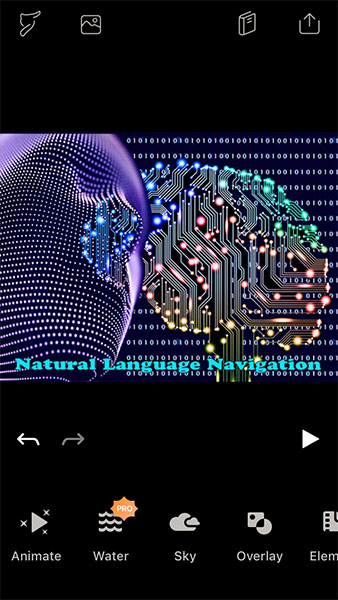
Enlight Pixaloop

This app from Lightricks carries a lot of promise to make your pictures stand out from the mundane images. But the free version has many of the advanced features crippled as expected. The free version lets you add sky to the background of your image and allows you to save that as an iPhone Live image or a Video file. Similarly it allows you to add overlays of some effects or add elements like butter fly amongst other things.
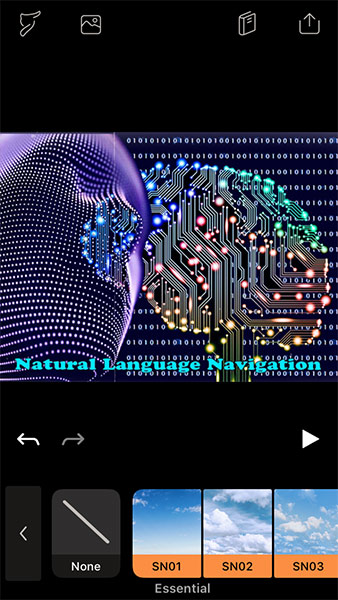
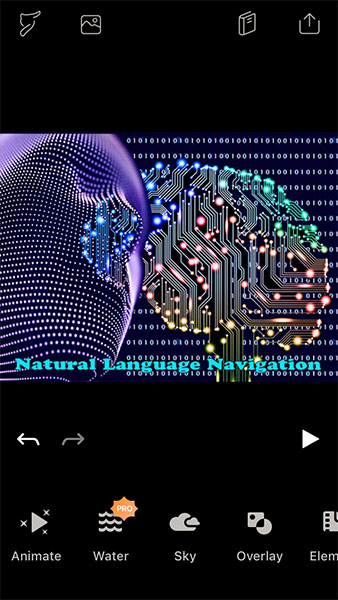
If you select an effect it shows you the working effects before you save them. I find the sky effect as appearing quite natural. The moving cloud effect really compares positively with that produced by professional software costing a pile of money. What is more, it takes pressing a few buttons to achieve the effect which would have taken hours. For animation, it is a hit and miss affair. When I tried to create a path for animation, it was not that precise. I realized this only when I saw the result in my 27 inch desk top monitor after exporting the results. For diminutive screen sizes, the animation may seem impressive, but check in a larger monitor before you share your files.
But truth be said, I have never been much of a fan of apps which try to imitate a seasoned Photographer or what you can achieve with the industry standard PhotoShop in a high end desktop computer. These apps depend on algorithms which shoehorn some preconceived �effects� into the image you have taken. In a basic way, it might appear to do the job effectively for the given effect. But nothing replaces a trained eye and professional software. Anyway these apps are probably not designed to replace a design professional � but to fill a basic need for just about everyone.